In an era where digital infrastructure underpins nearly every facet of American life from national defense and healthcare to banking and transportation, cybersecurity has become a cornerstone of national security and economic stability.
The United States faces an escalating array of cyber threats, ranging from sophisticated state-sponsored espionage to financially motivated ransomware attacks. As the digital landscape evolves, so too must the strategies and policies designed to protect it.
Seeing the increasing rate of cyberattacks, the United States is very concerned about cyber threats, and governmental or non-governmental organizations are now aware to protect their computer systems from cyberattacks.
Hospitals, banks, financial institutions, technical companies, and government agencies are now spending tons of dollars on cybersecurity infrastructure in order to protect their business mechanism and millions of data of the consumers.
Table of Contents
What is the Importance of Cybersecurity in the United States?
The importance of Cybersecurity in the United States is relevant. The entire world is a cyber threat today. Some types of cybercrimes have become common news these days.
The Escalating Threat Landscape
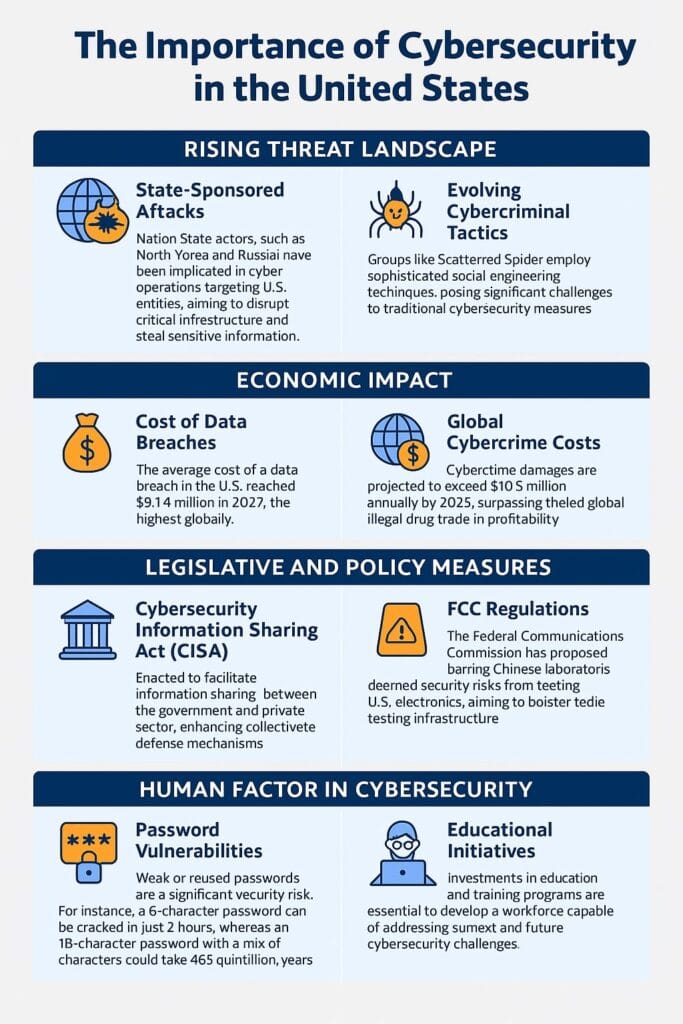
State-Sponsored Cyberattacks
Nation-state actors have increasingly leveraged cyber operations to achieve geopolitical objectives.
For instance, North Korean cyber operatives established fraudulent U.S. based companies to distribute malware targeting cryptocurrency developers, aiming to circumvent international sanctions and fund their nuclear program.
In the United States, many companies were heavily attacked by cybercrimes in the current year and the last few years.
Similarly, Russian military intelligence has been implicated in cyberattacks that combine traditional sabotage with modern cyber techniques, such as GPS spoofing and jamming, disrupting both civilian and military aviation operations .
The US Federal Government is now placing more emphasis on cybersecurity solutions in every governmental and non-governmental agency.
Critical Infrastructure Vulnerabilities
The 2021 ransomware attack on Colonial Pipeline by the DarkSide group underscored the susceptibility of critical infrastructure to cyber threats.
This incident led to widespread fuel shortages across the East Coast and prompted emergency declarations in 17 states. Such attacks highlight the potential for cyber incidents to cause tangible, real-world disruptions.
Emerging Cybercriminal Tactics
Cybercriminal groups like Scattered Spider have adopted unconventional methods, utilizing social engineering tactics and operating as loose collectives rather than traditional hierarchical organizations.
Their ability to infiltrate major corporations, including U.S. casinos and international retailers, demonstrates the evolving nature of cyber threats.
Economic Implications of Cyber Insecurity
Cybercrime imposes significant financial burdens on the U.S. economy. The average cost of a data breach in 2024 reached $4.88 million, marking a 10% increase from the previous year .
Globally, cybercrime damages are projected to exceed $6 trillion by the end of 2021, surpassing the economic impact of natural disasters and becoming more profitable than the global illegal drug trade.
These figures underscore the necessity for robust cybersecurity measures to protect economic interests.
Legislative and Policy Responses
Cybersecurity Information Sharing Act (CISA)
Enacted in 2015, CISA facilitates the sharing of cyber threat information between the federal government and private sector entities.
While proponents argue that it enhances collective defense mechanisms, critics express concerns over potential privacy infringements and the broad dissemination of personal data across government agencies .
National Cybersecurity Strategy
Released in 2023, the National Cybersecurity Strategy emphasizes reallocating cybersecurity responsibilities from individuals and small businesses to organizations better equipped to manage risks.
It advocates for long-term investments in cybersecurity infrastructure and promotes collaboration between public and private sectors to secure cyberspace .
Regulatory Measures
The Federal Communications Commission (FCC) has proposed barring Chinese laboratories deemed national security risks from testing electronic devices for U.S. use.
This move aims to close loopholes in the equipment authorization process and bolster domestic testing infrastructure.
The Human Element in Cybersecurity
Human behavior remains a critical factor in cybersecurity. Weak or reused passwords, for instance, can be exploited through brute-force attacks.
A report by Hive Systems revealed that a 5-character password using numbers and mixed-case letters can be cracked in just 2 hours, whereas an 18-character password with a mix of characters could take 463 quintillion years to break.
This highlights the importance of educating individuals on best practices for password creation and management.
Challenges in Workforce and Education
The demand for skilled cybersecurity professionals continues to outpace supply. A shortage of qualified personnel hampers the ability of organizations to defend against sophisticated cyber threats.
Investing in education and training programs is essential to develop a workforce capable of addressing current and future cybersecurity challenges.
Cybersecurity Strategies
The importance of Cybersecurity in the United States is widespread. Hence, cybersecurity is mandatory to keep your computer data safe from being leaked.
Protecting secret data is of paramount importance for defense, banking, intelligence and other sectors. To provide cybersecurity to the computer systems of individuals and agencies, Cybersecurity Strategies must be designed and implemented.
Right Cybersecurity Framework
In terms of cybersecurity strategies, organizations must choose the right framework for their cybersecurity strategies. This will steer the cybersecurity infrastructure in the right direction. If a wrong strategy is adopted, it only results in a loss of dollars and time.
Secure Cyber Ecosystem
The Cyber Ecosystem includes a wide range of different entities, such as computer devices, individuals, and organizations that interact with each other.
This strategy discovers the new idea of having a strong cyber-ecosystem that ensures the prevention of cyberattacks in situations when cyber-devices interact with each other and find the perfect solution to recover from a cyberattack.
This type of cyber-ecosystem would be able to create into its cyber tools to organize secure modes of action among groups of computers.
Conclusion
Cybersecurity is integral to the United States’ national security, economic prosperity, and the protection of individual privacy.
There is a growing awareness of the Importance of Cybersecurity in the United States, and therefore, a number of Cybersecurity Companies have emerged to provide individuals and businesses with the cybersecurity of their computer systems from cybercrimes.
As cyber threats become more sophisticated and pervasive, a comprehensive approach involving legislative action, public-private collaboration, workforce development, and public education is imperative.
By prioritizing cybersecurity, the United States can safeguard its digital infrastructure and maintain its position as a global leader in the digital age.