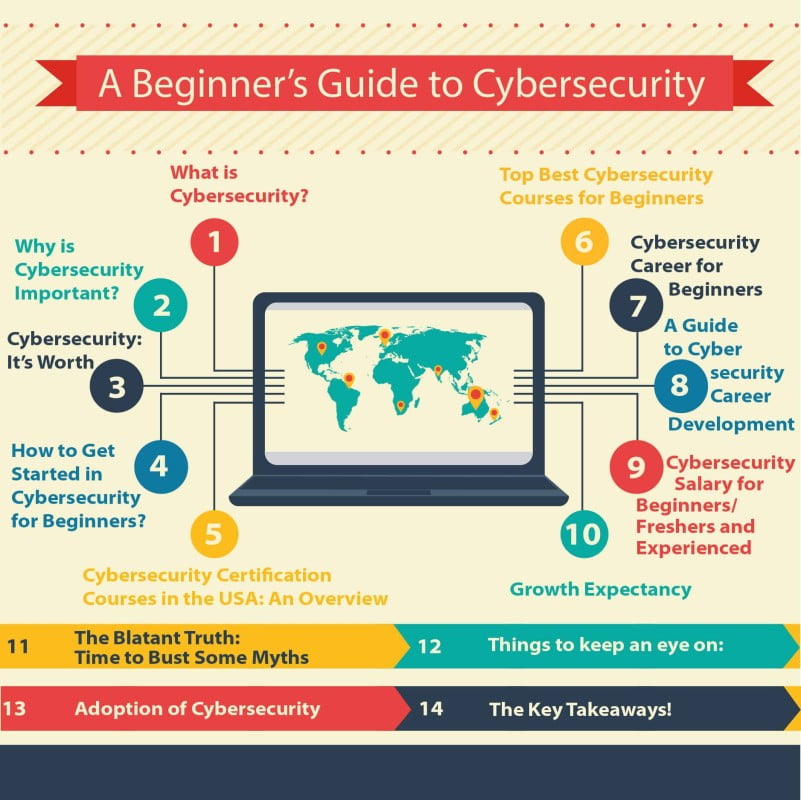
What is Cybersecurity? A Beginner’s Introduction
Cybersecurity for beginners starts with understanding one fundamental truth: protecting data, networks, and systems has become essential for every organization.
Cybersecurity is the practice of safeguarding computers, networks, programs, and data from unauthorized access, exploitation, and damage.
It encompasses the tools, policies, and procedures that organizations use to control access to resources, manage IT risk, and protect digital systems from evolving threats.
In simple terms, cybersecurity is information technology security. As cyber threats grow more sophisticated and widespread, governments and businesses worldwide now recognize cybersecurity as a critical priority.
For anyone exploring cybersecurity for beginners, this guide will walk you through everything you need to know from foundational concepts to career paths and certifications.
Many organizations have integrated information risk management into their daily operations to protect sensitive internal data. Understanding these practices is a key first step in learning cybersecurity for beginners.
Why Cybersecurity Matters
Cyber threats are evolving rapidly. From data breaches to ransomware attacks, organizations of all sizes face constant risk. Strong cybersecurity practices help:
- Protect sensitive customer and business data
- Maintain trust and reputation
- Ensure compliance with regulations
- Prevent financial losses from cyber incidents
Universities and colleges have responded by developing specialized cybersecurity programs, often designed with input from industry experts to equip professionals with both theoretical knowledge and hands-on skills. For those new to the field, cybersecurity for beginners programs have never been more accessible.
Is Cybersecurity Right for You?
A career in cybersecurity can be rewarding both intellectually and financially. Many entry-level and mid-level roles offer competitive salaries, and demand for qualified professionals continues to outpace supply. If you are considering cybersecurity for beginners as a career path, you are entering one of the fastest-growing fields in technology.
Successful cybersecurity practitioners typically possess:
| Skill | Why It Matters |
| Attention to Detail | Spotting subtle anomalies can prevent major breaches |
| Problem-Solving Skills | Finding creative solutions to complex security challenges |
| Analytical Thinking | Understanding how systems and attackers behave |
| Passion for Learning | The cybersecurity landscape evolves constantly |
The industry offers diverse career paths, from technical roles like penetration testing to leadership positions such as Chief Information Security Officer (CISO). Online quizzes and self-assessment tools can help you determine if cybersecurity for beginners aligns with your skills and interests.
How to Get Started in Cybersecurity for Beginners
There has never been a better time to enter the cybersecurity field. A significant skills gap means there are more jobs than qualified candidates creating tremendous opportunity for newcomers. Cybersecurity for beginners is not just about technical skills; it requires a well-rounded approach.
Aspiring cybersecurity professionals should be prepared to engage with a variety of disciplines:
| Technical Areas | Foundational Skills |
| Network security | Communication |
| Application security | Problem-solving |
| Cryptography | Critical thinking |
| Incident response | Business acumen |
| Cloud security | Policy and compliance |
How to Start Learning Cybersecurity as a Beginner
If you are wondering how to learn cybersecurity for beginners, here are practical ways to begin your journey:
📚 Learn from Books
Numerous cybersecurity books are available, from introductory guides to advanced technical manuals. Reading helps you understand digital networks, device communication, and security principles. This is often the first step in cybersecurity for beginners education.
🌐 Follow Industry Experts Online
Leading professionals regularly publish articles, blogs, and research. Following these voices helps you stay current and exposes you to diverse perspectives. Many experts share free resources specifically for cybersecurity for beginners.
🛡️ Explore Ethical Hacking
Understanding how attackers operate is one of the most effective ways to defend against them. Ethical hacking courses allow you to think like an adversary and anticipate risks. This hands-on approach is invaluable for cybersecurity for beginners.
🎓 Enroll in Specialized Courses
Many universities and online platforms offer programs in information technology and cybersecurity. Career changers will also find certificate programs designed to facilitate a smooth transition. Look for courses labeled cybersecurity for beginners to ensure appropriate pacing.
Free Resources for Beginners
You do not need to spend money to start learning. Here are some of the best free resources available for cybersecurity for beginners:
| Resource | Description |
| TryHackMe | Free hands-on cybersecurity labs and beginner-friendly rooms |
| Cybrary | Free courses covering fundamentals, certifications, and tools |
| OWASP | Open-source web application security resources and guides |
| YouTube | Channels like NetworkChuck, The Cyber Mentor, and Professor Messer |
| NIST Cybersecurity Framework | Free industry standards and guidelines from the U.S. government |
| CISA | Cybersecurity & Infrastructure Security Agency free training |
| Open Security Training | Free, in-depth security training courses |
These free resources allow you to explore the field before committing to paid courses or certifications.
Where to Start: A Learning Path for Beginners
With so many options available, this structured path can help you build a solid foundation for cybersecurity for beginners:
Network Security Basics
Learn how computer networks function. Key topics include TCP/IP, firewalls, routing, and switching. Understanding network fundamentals helps you identify and address threats. This is a core component of any cybersecurity for beginners curriculum.
Application Security and Vulnerabilities
Explore how applications work and common weaknesses. Topics include insecure coding practices, software vulnerabilities, and how applications interact with networks. Mastering these concepts elevates your cybersecurity for beginners knowledge.
Penetration Testing and Offensive Security
Study penetration testing, social engineering, wireless security, and hardware hacking. Understanding attacker tactics strengthens your defensive capabilities. Many cybersecurity for beginners programs introduce these concepts gradually.
Core Cybersecurity Concepts
With a foundation in networks and applications, you can begin implementing security measures such as access controls, monitoring, and incident response. This is where cybersecurity for beginners transitions from theory to practice.
The Best Way to Learn Cybersecurity for Beginners
✅ Start with Fundamentals
Focus on clean, secure practices. Hands-on experience is one of the most effective ways to learn. For cybersecurity for beginners, starting with fundamentals ensures long-term success.
✅ Take an Online Course
Structured courses taught by industry professionals provide clear learning paths and often include certification preparation. Many platforms offer cybersecurity for beginners courses with flexible schedules.
✅ Commit to Continuous Learning
Cybersecurity evolves rapidly. Stay current by following industry news, attending webinars, and participating in online communities. Cybersecurity for beginners is just the start—ongoing education is essential.
✅ Build Hands-On Skills
Practical experience is critical. Setting up a home lab, participating in Capture The Flag (CTF) competitions, and building a portfolio will set you apart.
Basic Skills You Need for Cybersecurity
If you are pursuing cybersecurity for beginners, these foundational skills will serve you well:
| Skill | Why It Matters |
| Problem-Solving | Troubleshooting malware, vulnerabilities, and user errors |
| Written Communication | Documenting activities and explaining security concepts clearly |
| Technical Aptitude | Understanding networking, operating systems, and databases |
| Security Clearance | Required for some government and defense roles |
| Specialized Training | Role-specific skills gained through courses and certifications |
Degrees, Courses, and Certifications for Beginners
A degree in computer science or information technology is a common starting point. Many U.S. universities offer online bachelor’s and master’s programs in cybersecurity for flexibility. However, cybersecurity for beginners does not always require a degree—certifications and bootcamps are excellent alternatives.
Popular learning paths include:
- Bachelor’s Degree in Cybersecurity
- Master’s Degree in Cybersecurity
- Online Master’s Programs
- Cybersecurity Bootcamps
- PhD in Cybersecurity
Top Cybersecurity Certifications for Beginners
| Certification | Best For |
| CompTIA Security+ | Foundational knowledge; ideal for cybersecurity for beginners |
| Certified Ethical Hacker (CEH) | Offensive security and penetration testing |
| GIAC Security Essentials (GSEC) | Hands-on security management skills |
| CISM | Security management (requires experience) |
| CISSP | Advanced roles (requires 5+ years experience) |
The National Initiative for Cybersecurity Education (NICE) , part of NIST, provides a framework that aligns with many of these certifications to help beginners map their skills to industry-recognized roles. Other valuable certifications include GPEN, CRISC, CISA, and CCSP.
Entry-Level Cybersecurity Jobs
If you are pursuing cybersecurity for beginners, here are common entry-level job titles to target:
| Job Title | Typical Responsibilities |
| Security Analyst | Monitor networks, investigate security alerts, respond to incidents |
| SOC Analyst | Work in a Security Operations Center monitoring threats |
| IT Support Specialist | Entry point with security focus; troubleshoot and secure systems |
| Network Administrator | Manage and secure network infrastructure |
| Compliance Analyst | Ensure organizations follow security policies and regulations |
| Junior Penetration Tester | Assist in ethical hacking and vulnerability assessments |
| Security Administrator | Manage user access, firewalls, and security tools |
These roles provide valuable experience and serve as stepping stones to more advanced positions.
How to Build Experience (No Experience Needed)
One of the biggest challenges for cybersecurity for beginners is gaining experience without having a job first. Here are practical ways to build your skills and portfolio:
🎯 Capture The Flag (CTF) Competitions
Participate in free CTF events on platforms like:
- CTFtime – Global competition calendar
- PicoCTF – Beginner-friendly educational CTF
- HackTheBox – Free tier available
🏠 Build a Home Lab
Set up a practice environment using:
- VirtualBox or VMware (free virtualization)
- Kali Linux (security testing OS)
- SIEM tools like Splunk Free
- Firewalls like pfSense
📝 Open-Source Contributions
Contribute to security-related open-source projects. This demonstrates real-world collaboration and technical skills.
🤝 Volunteer
Offer security services to:
- Local nonprofits
- Community organizations
- Small businesses
- Religious institutions
✍️ Blog or Document Your Journey
Create a blog, LinkedIn posts, or GitHub repository documenting:
- Labs you have completed
- CTF write-ups
- Tools you have learned
- Certifications earned
This creates a public portfolio that employers can review, even without formal work experience.
Cybersecurity Career Paths
Cybersecurity professionals work across industries including finance, government, healthcare, retail, and technology. For those starting with cybersecurity for beginners, understanding career paths helps with long-term planning.
Typical Career Progression
| Entry-Level | Mid-Level | Senior/Executive |
|---|---|---|
| Security Analyst | Security Engineer | Security Architect |
| Network Administrator | Penetration Tester | Security Manager |
| IT Support Specialist | Incident Responder | CISO |
| Junior SOC Analyst | Threat Hunter | Director of Security |
Many professionals transition into cybersecurity after gaining 3–5 years of general IT experience. A background in infrastructure or development can significantly improve your job prospects. Cybersecurity for beginners often serves as a gateway for IT professionals seeking specialization.
What Cybersecurity Professionals Do
- Monitor, test, and troubleshoot security systems
- Install and operate security devices
- Develop security policies and procedures
- Educate employees on safe practices
- Respond to incidents and breaches
- Conduct risk assessments and compliance audits
Cybersecurity Salaries: A Snapshot
Cybersecurity professionals are well-compensated due to high demand and a persistent skills gap. Even for those entering through cybersecurity for beginners programs, salary potential is strong.
- Entry-level positions typically start between $60,000–$85,000
- Mid-level roles range from $85,000–$120,000
- Senior and executive roles often exceed $150,000, with top positions like CISO reaching $200,000+ in major markets
According to the U.S. Bureau of Labor Statistics, information security analysts earn a median salary of over $98,000, with job growth projected at 31%—much faster than the national average.
Job Growth and Industry Outlook
Cyber threats continue to evolve, and demand for cybersecurity professionals remains strong. The growing reliance on cloud computing, mobile devices, and connected systems ensures that cybersecurity expertise will be essential for the foreseeable future. Cybersecurity for beginners today positions you for long-term career stability.
Key growth areas include:
- Cloud Security – Protecting cloud-based applications and infrastructure
- Internet of Things (IoT) – Securing connected devices
- AI and Machine Learning – Using automation to detect and respond to threats
- Encryption Technology – Safeguarding sensitive data
- Zero Trust Architecture – Emerging security framework
Common Myths About Cybersecurity for Beginners
🧢 Myth: Cybersecurity Is All About Hacking
The image of a lone hacker in a hoodie is a popular stereotype but far from reality. Cybersecurity for beginners encompasses policy development, risk management, compliance, training, and incident response.
🎓 Myth: You Need a Computer Science Degree to Get Started
While a degree can be helpful, it is not the only path. Many professionals enter through certifications, bootcamps, self-study, or by transitioning from other IT roles. Cybersecurity for beginners is accessible to motivated learners from all backgrounds.
💻 Myth: You Must Be a Programming Expert
Not all cybersecurity roles require coding. While programming helps for some positions, many roles focus on networking, governance, compliance, or operations.
🔒 Myth: You Need Years of Experience to Start
Entry-level roles, internships, and apprenticeships exist specifically for beginners. Combined with home labs, CTFs, and certifications, you can build a competitive resume without formal experience.
Conclusion: Your Cybersecurity Journey Starts Now
Cybersecurity for beginners may seem overwhelming at first, but every expert was once a beginner. The field offers immense opportunity for those willing to learn, practice, and persist.
Throughout this guide, we have covered the fundamentals of cybersecurity, how to determine if this career aligns with your goals, practical ways to start learning, a structured path from basics to core concepts, essential certifications, entry-level job titles, and how to build experience without a prior IT background.
Demand for cybersecurity professionals continues to grow, and the skills gap means opportunities are abundant for those who take the first step.
Whether you choose self-study, certifications, or a formal degree, start today. Build your home lab, join a CTF competition, enroll in a course, and connect with the cybersecurity community. Every small step builds momentum toward a rewarding career protecting the digital world.
Frequently Asked Questions
What is the best way to learn cybersecurity for beginners?
Combine hands-on practice with structured learning. Start with fundamentals, take a certification course like CompTIA Security+, and build your own lab environment to gain practical experience. Cybersecurity for beginners resources are widely available online.
What do I need to know before starting cybersecurity?
A basic understanding of computer networks, operating systems, and general IT concepts is helpful. However, many cybersecurity for beginners resources assume no prior knowledge, making the field accessible to motivated beginners.
How long does it take to start a career in cybersecurity?
With focused effort, many beginners land entry-level roles within 6–12 months through certifications, and practical experience. The timeline varies based on prior IT background and time commitment.