In an increasingly digital world, encountering malware is not a matter of if, but when. This malicious software is one of the most pervasive threats facing anyone with an internet-connected device.
It’s a troubling issue that most of us will likely face, often not as a targeted attack, but as a random, indiscriminate act of cybercrime. The impact, however, is anything but random.
Once a device is infected with malware, it can trigger a cascade of problems. You might experience a frustrating decline in your computer’s performance, or face a catastrophic financial loss if the malware steals sensitive data like banking credentials.
In this comprehensive guide, we will explore what malware is, how it has evolved, the different types you need to watch out for in 2026, and most importantly the actionable steps you can take to protect yourself and your devices.
What is a Malware?
Malware, short for malicious software, is a blanket term for any code or program intentionally designed to infiltrate, disrupt, damage, or disable computer systems, networks, and devices without the owner’s informed consent.
It operates covertly to compromise normal computer functions, steal data, gain unauthorized access, or hijack system resources.
The threat of malware is not new. It has been around since the 1970s with the “Creeper” virus, and the danger to both individuals and organizations has only intensified since then. Malware can exist as a file or a code snippet transferred to a system through a network.
Its penetration often leads to a noticeable decline in system performance, frequent error messages, and a generally hindered user experience.
Malware vs. Faulty Software: A Critical Distinction
It is important to distinguish malware from faulty software. Legitimate software sometimes contains bugs or errors that were not fixed before release, leading to crashes or security vulnerabilities.
However, these are unintentional. Malware, in contrast, is intentionally created with malicious intent to steal, damage, or extort.
What Does Malware Do?
The primary goal of malware is to benefit its developer, often at the significant expense of the user. It achieves this by:
Stealing Sensitive Information
Malware can spy on your online activities, capture keystrokes to log passwords, and scan your system for financial data or personal documents.
Disrupting Operations
From slowing down your computer to encrypting all your files and holding them hostage, malware can bring productivity to a halt.
Gaining Unauthorized Access
Some malware creates “backdoors,” giving hackers remote control over your machine to use it for further attacks.
Hijacking System Resources
Your computer can be silently conscripted into a botnet, a network of infected devices used to launch massive Distributed Denial of Service (DDoS) attacks against websites or mine cryptocurrency without your knowledge.
15 Different Types of Malware to Know in 2026
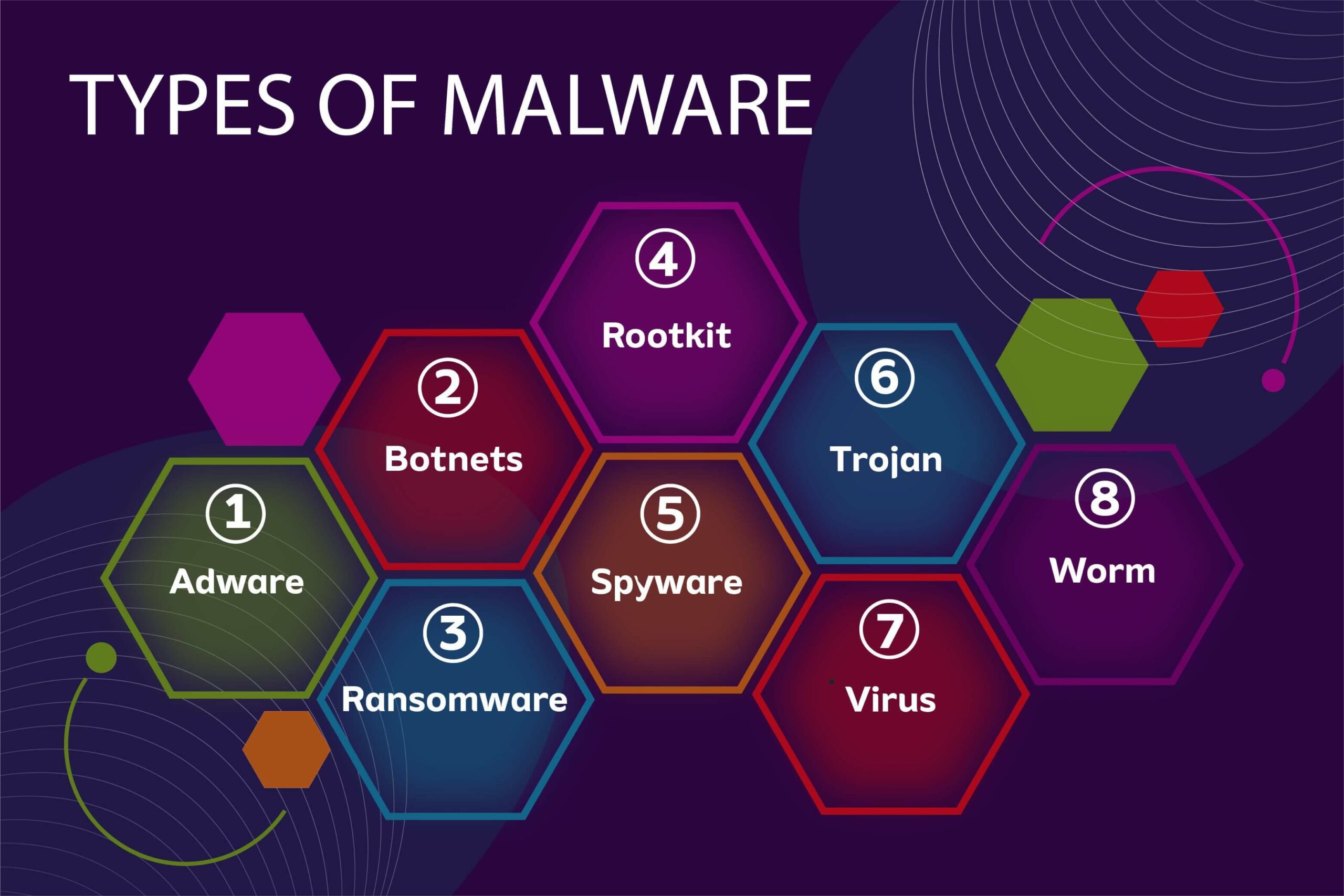
The world of malware is diverse and constantly evolving, with new variants and hybrids appearing regularly.
In 2026, cybercriminals are leveraging artificial intelligence to create more adaptive and harder-to-detect threats. Here are the 15 most important malware types you need to understand to stay protected.
1. Virus
A virus is one of the oldest and most recognized forms of malware. It functions by attaching its malicious code to clean files or programs.
When the infected file is executed by you or the system, the virus activates, spread to other files and programs on the host computer.
Viruses require human intervention (like opening an infected email attachment or running a downloaded program) to propagate and cause damage. They can corrupt data, degrade system performance, and provide a gateway for other malware.
2. Worm
A worm is similar to a virus in its ability to replicate, but with one critical difference: it is self-sufficient.
Worms can spread across networks and devices automatically, without any human action. They exploit vulnerabilities in operating systems and software to propagate from machine to machine.
Once inside a network, a worm can consume massive bandwidth, overload servers, and drop payloads (like ransomware or backdoors) on infected systems. The infamous Conficker and WannaCry attacks were worms that caused billions in damages.
3. Trojan Horse
Named after the ancient Greek story, a Trojan horse disguises itself as legitimate, desirable, or useful software such as a free antivirus program, a popular game, or a system update tool. Users willingly download and install it, unaware of its hidden malicious purpose.
Unlike viruses and worms, Trojans do not self-replicate. Instead, they create backdoors, steal sensitive data, download other malware, or spy on user activity.
4. Ransomware
Ransomware is one of the most financially devastating types of malware. It encrypts a victim’s files, folders, or even entire hard drives, making them inaccessible.
The attacker then demands a ransom payment, typically in cryptocurrency like Bitcoin, in exchange for the decryption key. In some cases, attackers also exfiltrate sensitive data and threaten to leak it unless paid (a tactic known as “double extortion” ).
According to the 2025 Global Threat Report, ransomware attacks increased by 67% year-over-year, with threat actors targeting critical infrastructure, healthcare, and education sectors.
Paying the ransom is discouraged by law enforcement and security experts, as there is no guarantee you will regain access to your data.
5. Spyware
As the name implies, spyware is designed to spy on you without your knowledge or consent. It secretly monitors your online activities, including websites visited, search queries, emails sent, and keystrokes typed.
This information is then transmitted to a third party, often for identity theft, fraud, or targeted advertising. Some spyware, like Pegasus developed by the NSO Group, is sophisticated enough to infect smartphones and extract messages, photos, and even record calls.
6. Adware
Adware is malware that automatically delivers unwanted advertisements to a user. While often considered more annoying than dangerous, adware can significantly degrade system performance and user experience.
More concerning is its frequent combination with spyware; adware tracks your browsing habits to serve targeted pop-up ads, and those ads can sometimes lead to malicious websites.
Malvertising (malicious advertising) uses legitimate ad networks to distribute ads containing hidden malware, infecting users who simply view the ad.
7. Rootkit
A rootkit is a collection of software tools designed to gain and maintain administrator-level (or “root”) access to a computer while actively concealing its presence.
Rootkits can hide files, processes, and network connections from standard security tools, making them exceptionally difficult to detect. They often load before the operating system boots, embedding themselves deep within the system firmware, hypervisors, or kernel.
Once installed, a rootkit can be used to disable security software, steal sensitive data, and provide a covert channel for attackers to control the machine remotely.
8. Backdoor / Remote Access Trojan (RAT)
A backdoor is a method of bypassing normal authentication or encryption in a system. Malware that installs a backdoor is often called a Remote Access Trojan (RAT).
Once a RAT is installed, it opens a hidden communication port, allowing an attacker to remotely control the victim’s computer as if they were sitting in front of it.
This access can be used to steal files, monitor user activity, activate the webcam or microphone, and use the infected machine as a launchpad for attacks on other systems.
9. Keyloggers
A keylogger (short for keystroke logger) is a type of system monitor that records every key pressed on a keyboard.
This allows attackers to capture a staggering amount of sensitive information, including usernames, passwords, credit card numbers, personal emails, and instant messages.
While some keyloggers are hardware devices, most are software-based and can be installed through phishing emails, malicious downloads, or drive-by downloads.
Businesses may use keyloggers legitimately to monitor employee activity, but when installed maliciously, their purpose is almost always data theft.
10. Fileless Malware
Considered an advanced and evasive threat, fileless malware operates in a computer’s memory (RAM) rather than using traditional files on the hard drive.
It often leverages legitimate system administration tools already present on the machine, such as PowerShell, WMI (Windows Management Instrumentation), or .NET frameworks, to execute its malicious code.
Because it doesn’t write files to disk, fileless malware can evade traditional signature-based antivirus software, making it significantly harder to detect and remove.
11. Bots and Botnets
A bot (short for robot) is a computer or device infected with malware that allows it to be controlled remotely by an attacker, often without the user’s knowledge. A botnet is a vast network of these infected, coordinated devices, controlled by a “bot herder.”
Botnets are used for large-scale cybercriminal activities, including launching Distributed Denial of Service (DDoS) attacks (overwhelming a website with traffic), sending massive spam email campaigns, spreading new malware, and performing credential-stuffing attacks.
12. Cryptojacker
Cryptojacking (also called malicious cryptocurrency mining) is a type of malware that secretly uses a victim’s computing resources (CPU and GPU power, electricity) to mine for cryptocurrencies.
The malware runs silently in the background, often causing significant system slowdowns, overheating, increased fan noise, and higher electricity bills for the victim. The attacker, meanwhile, collects the mined coins.
Cryptojacking can occur through malicious downloads or even via malicious scripts embedded in websites that run while the user’s browser is open.
13. Wiper
Unlike most malware, which aims to steal data or extort money, a wiper is designed with the singular purpose of destroying data and rendering systems inoperable.
Wipers overwrite files, corrupt system functions, and can even damage hardware by flashing malicious firmware.
They are often used in targeted attacks, hacktivism, or state-sponsored cyber warfare to cause maximum disruption and chaos. Notable examples include NotPetya and the attacks on Ukraine’s power grid.
14. Scareware
Scareware uses social engineering and psychological manipulation specifically, fear to trick users into taking unwanted actions.
It typically presents fake, alarming warnings claiming the computer is infected with numerous viruses or that illegal activity has been detected on the system.
The user is then prompted to purchase a (usually useless) “security” tool, share personal information, or call a fake tech support number to resolve the non-existent issue.
15. Logic Bomb
A logic bomb is a piece of malicious code that is secretly inserted into a software system and lies dormant until a specific condition or trigger is met.
This trigger could be a date, a time, a user action (like logging in), or the absence of a certain file (like an employee’s credentials being removed from the system).
When the condition is satisfied, the logic bomb “explodes,” delivering its payload which could be anything from deleting critical data to corrupting system files. Logic bombs are often planted by disgruntled employees with inside access to a company’s systems.
How To Prevent Malware Attacks?
As cybersecurity experts note, “A single security solution can’t address all threats.” Here are the essential strategies to build a robust defense.
1. Strengthen Your Digital Defenses: The Tech Layer
Install and Maintain Robust Security Software
Your first line of defense is high-quality anti-malware software. This should offer real-time protection, behavioral analysis, and frequent signature updates.
For Windows users, ensure Windows Defender (now a robust security suite) is activated and configured for real-time protection. You can also layer it with reputable third-party tools like Malwarebytes for periodic on-demand scans.
Enable and Configure Your Firewall
A firewall acts as a gatekeeper between your device and the internet, monitoring incoming and outgoing traffic based on a set of security rules. Ensure your operating system’s firewall is turned on and properly configured.
This helps block unauthorized access and can prevent malware from communicating with its command-and-control servers.
Keep Everything Updated
Cybercriminals love exploiting known vulnerabilities in outdated software. The best defense is to enable automatic updates for your operating system, web browsers, plugins, and all installed applications. Patching these holes is one of the simplest yet most critical security steps.
2. Practice Safe Browsing: The Behavior Layer
Technology alone can’t protect you from your own actions. Safe online behavior is your digital immune system.
Become an Expert at Spotting Phishing
Be extremely cautious with emails, messages, or attachments from unknown senders. Do not click on links or open attachments in unsolicited messages. Remember, phishing attacks are designed to create a false sense of urgency or fear.
Verify Before You Click
Hover your mouse over links to see the actual destination URL before clicking. Be wary of shortened links. If an offer seems too good to be true, it probably is.
As a rule of thumb, avoid visiting suspicious websites, particularly those associated with illegal activities like piracy, as they are often hotbeds for “malvertising” (malicious advertising).
Download Software Only from Official Sources
Never download software from third-party sites, peer-to-peer networks, or dubious pop-up ads. Always stick to official app stores or the developer’s official website.
3. Understand Your Tools: The Knowledge Layer
To avoid common misconceptions, it’s vital to understand what your security tools actually do.
VPN vs. Antivirus: You Need Both
A VPN (Virtual Private Network) encrypts your internet connection and masks your IP address. This is crucial for privacy, especially on public Wi-Fi, as it prevents snoops from intercepting your traffic.
However, a VPN is not a replacement for antivirus software. A VPN secures your connection, while antivirus software secures your device by stopping malicious files from executing.
As one expert puts it, “A VPN is like closing the curtains to keep people from seeing inside, while an antivirus is like having a security system that stops intruders.” For full protection, you must use both.
4. Prepare for the Worst: The Resilience Layer
Even with the best precautions, a sophisticated attack might succeed. This is where resilience comes in.
Segment Your Network
If you have multiple devices, consider network segmentation. For example, keep IoT devices (smart TVs, cameras) on a separate Wi-Fi network from your main computers. This prevents malware from spreading laterally if one device is compromised.
Implement the Principle of Least Privilege
Use standard, non-administrator accounts for your daily work. If malware does infect your machine, it will have limited permissions and won’t be able to make system-wide changes.
Regularly Back Up Your Data
This is your ultimate safety net. Perform regular backups of all your important files and ensure the backup copies are stored offline or in a secure cloud service that retains previous versions of files.
In the event of a ransomware attack, a clean backup is often the only way to recover your data without paying a ransom.
Malware Prevention Checklist
| Category | Action Item | Key Benefit |
| Tech | Install & update anti-malware software. | Detects and removes known and emerging threats. |
| Tech | Enable firewall and automatic OS/software updates. | Blocks unauthorized access & patches vulnerabilities. |
| Behavior | Never click suspicious links or email attachments. | Prevents the most common entry point for malware. |
| Behavior | Download software only from official sources. | Avoids trojans and other malware disguised as apps. |
| Knowledge | Use a VPN on public Wi-Fi, but don’t skip antivirus. | Protects both your privacy (VPN) and your device (AV). |
| Resilience | Maintain off-line or secure cloud backups. | Allows data recovery without paying ransomware demands. |
What to Do If You Suspect a Malware Infection?
If your computer starts acting strangely—running slowly, displaying unexpected pop-ups, crashing frequently, or showing a sudden increase in network activity—you may be infected. Act quickly using these steps:
Isolate the System
Immediately disconnect the computer from the internet and any local networks to prevent the malware from spreading or communicating with its command center.
Enter Safe Mode
Reboot your computer in Safe Mode. This loads only the essential drivers and may prevent some malware from loading automatically.
Scan for Malware
Run a full system scan using your installed anti-malware software. If you don’t have any, you can download a reputable on-demand scanner on a clean computer and transfer it via USB.
Restore from Backup
If the scan fails to remove the infection or your files are encrypted, the most secure way to recover is to wipe the system and restore your data from a clean, offline backup taken before the infection.
Conclusion
Malware remains a dominant and evolving threat in 2026, with attackers constantly refining their methods to bypass traditional defenses. The key takeaway is that protection is no longer a single product but a layered strategy.
By combining robust technical defenses like updated anti-malware software and firewalls, practicing safe online behavior, understanding the role of tools like VPNs, and maintaining secure backups, you can drastically reduce your risk.
Frequently Asked Questions
Can malware steal passwords?
Yes. Keyloggers and spyware are specifically designed to capture keystrokes and monitor activity to steal passwords, usernames, and other login credentials.
Is malware the same as a virus?
No. A virus is just one specific type of malware. Malware is the broader category that includes viruses, worms, ransomware, spyware, Trojans, and many others.
Can smartphones get malware?
Absolutely. Smartphones are vulnerable to malware, often through malicious apps downloaded from unofficial app stores, phishing links in text messages, or compromised Wi-Fi networks.